Lab Activities & Seminar
Those section include any kind of activties about CyberSecurity so basicly I simulated every kind of Cyber Attack
Lab Activities
Activity-1:Scanning

Exploring Network Security: A Scanning Activity
In my journey to understand the complexities of network security, I recently completed a scanning activity that provided me with hands-on experience in identifying and analyzing security threats and vulnerabilities in network systems. This activity was not just an exercise, but a practical application of the theories and concepts I've been learning.
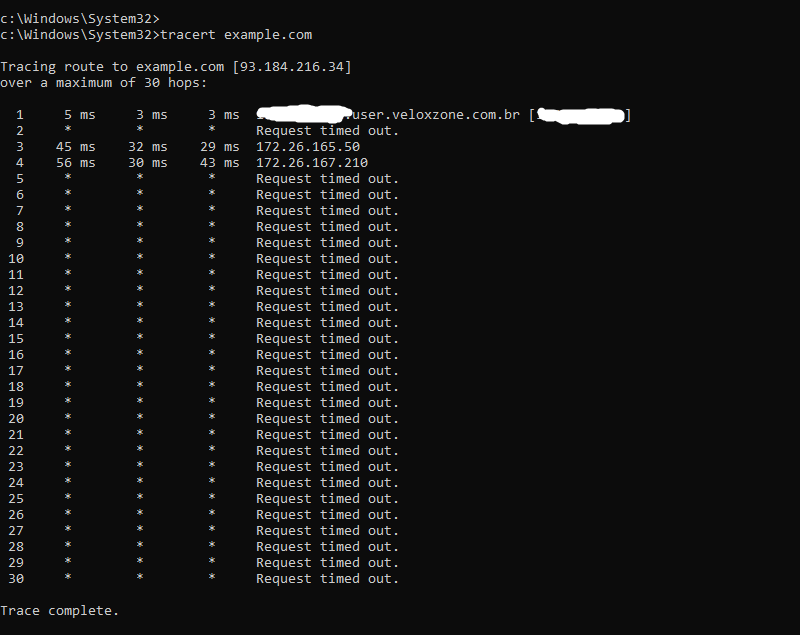
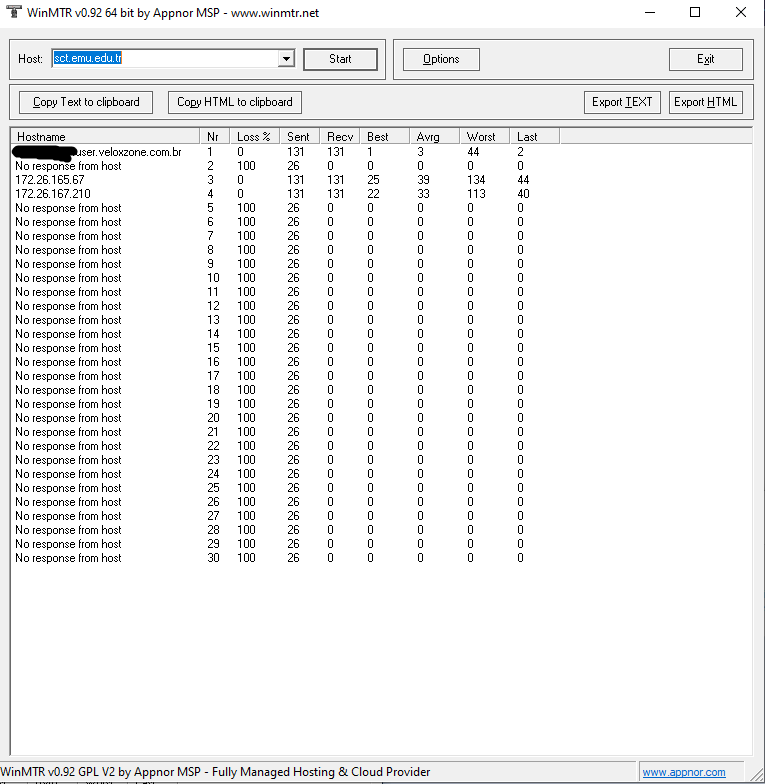
The task involved using standard tools such as traceroute, dig, and nslookup to perform a basic scan on an assigned website. This process allowed me to understand the intricacies of network communication and the potential vulnerabilities that could be exploited by malicious entities.
During the scan, I was required to gather specific information, such as the number of hops from my machine to the assigned website, the step causing the biggest delay in the route, the main nameservers for the website, the registered contact, the MX record, and the location where the website is hosted. This information is crucial in understanding the structure and vulnerabilities of a network system.
This activity was not without its challenges. However, overcoming these challenges provided me with valuable insights into the practical aspects of network security. It enhanced my problem-solving skills and my ability to use specific tools and techniques to manage and solve security threats.
One of the most significant learning outcomes from this activity was the ability to gather and synthesize information from multiple sources. This skill is particularly useful in the systematic analysis of security breaches and issues, as it allows for a comprehensive understanding of the situation.
Reflecting on this activity, I realize that it has equipped me with the knowledge and skills to design and critically appraise computer programs and systems to produce solutions that help manage and audit risk and security issues. It was a step forward in my journey to becoming a proficient network security professional.
In conclusion, this scanning activity was an enriching and enlightening experience. It provided me with a deeper understanding of network security and the practical skills to identify and address potential threats and vulnerabilities. I look forward to applying these skills in future projects and professional scenarios.
Activity-2:Honey Pot
Understanding Cybersecurity: A Honeypot Activity
In my ongoing exploration of cybersecurity, I recently engaged in a hands-on activity involving the setup and operation of a honeypot system. A honeypot is a computer system designed to lure and trap cyber attackers attempting to gain unauthorized access to information systems. This activity offered practical insights into the mechanisms of cybersecurity and the strategies used to deter potential threats.
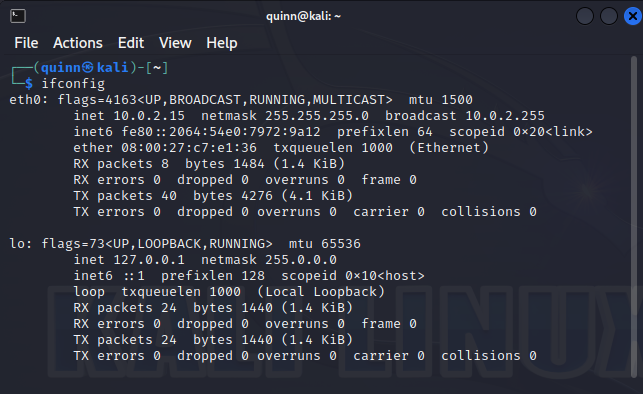
The task required me to navigate through a series of steps using the Terminal window. I started by executing the 'ifconfig' command to note down the inet IP of the eth0 router, a crucial piece of information for the later stages of the activity.
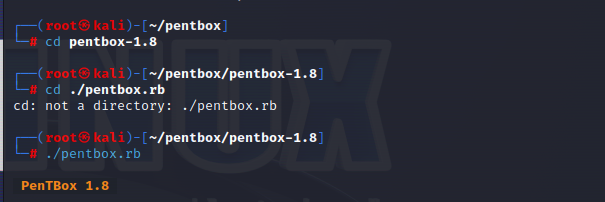
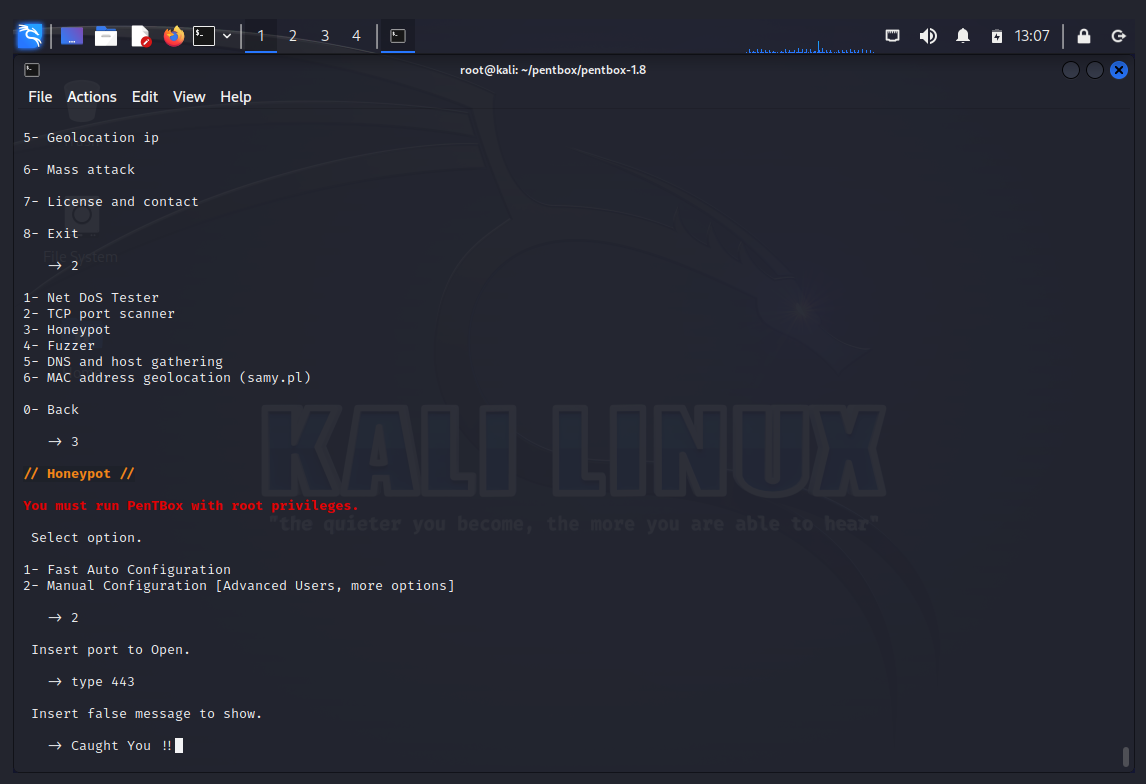
Next, I navigated to the pentbox-1.8 directory and ran the pentbox.rb script. This led me to a series of options, where I selected 'Network tools' and then 'Honeypot'. I opted for manual configuration to gain a deeper understanding of the process.
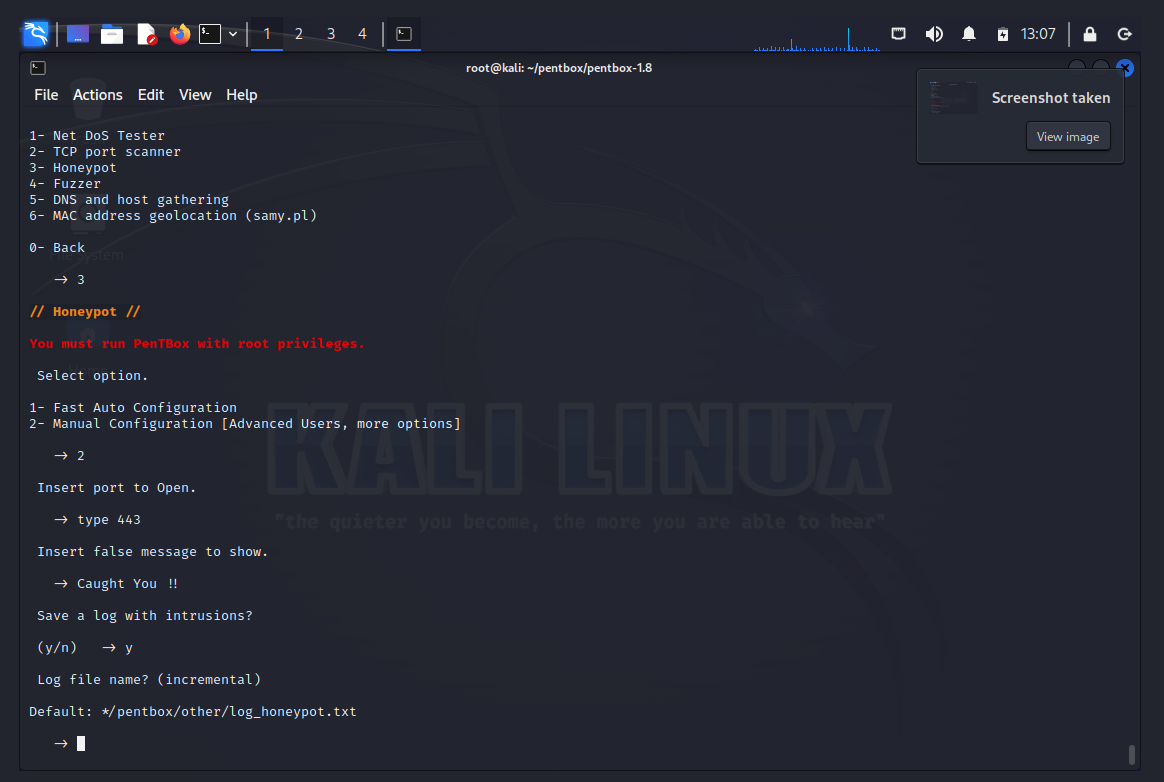
I then opened port 443 and set up a false message, "Caught You!!", designed to be displayed to any unauthorized user attempting to access the system. This step demonstrated the deceptive nature of honeypots and their role in deterring cyber attackers.
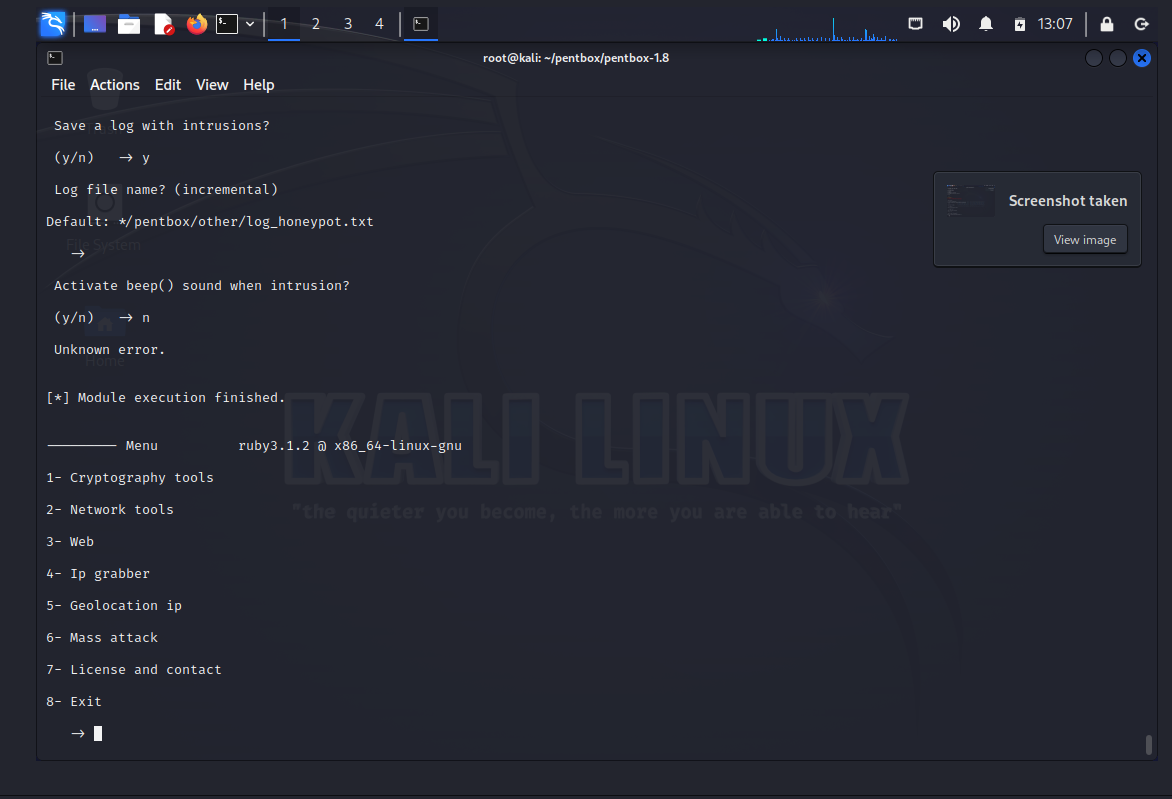
To ensure I had a record of the activity, I chose to save the log of the operation. This log serves as a valuable resource for reviewing the process and outcomes of the honeypot setup. I decided to save thelog file in the default location for easy access and opted not to activate the beep sound, demonstrating the customizable nature of honeypot systems.
Reflecting on this activity, I gained a deeper understanding of the strategic role of honeypots in cybersecurity. Setting up and operating a honeypot system provided me with practical experience in managing potential cyber threats. It also enhanced my technical skills and understanding of network systems.
Overall, the honeypot activity was an extremely beneficial experience that taught me invaluable lessons. It reinforced my existing theoretical knowledge and provided practical expertise that will surely help shape my future pursuits within cybersecurity. I am enthusiastic about exploring this captivating domain even more and putting these acquired skills into practice in realistic settings.
Activity-3:DDoS
Delving into Cybersecurity: A DDoS Activity
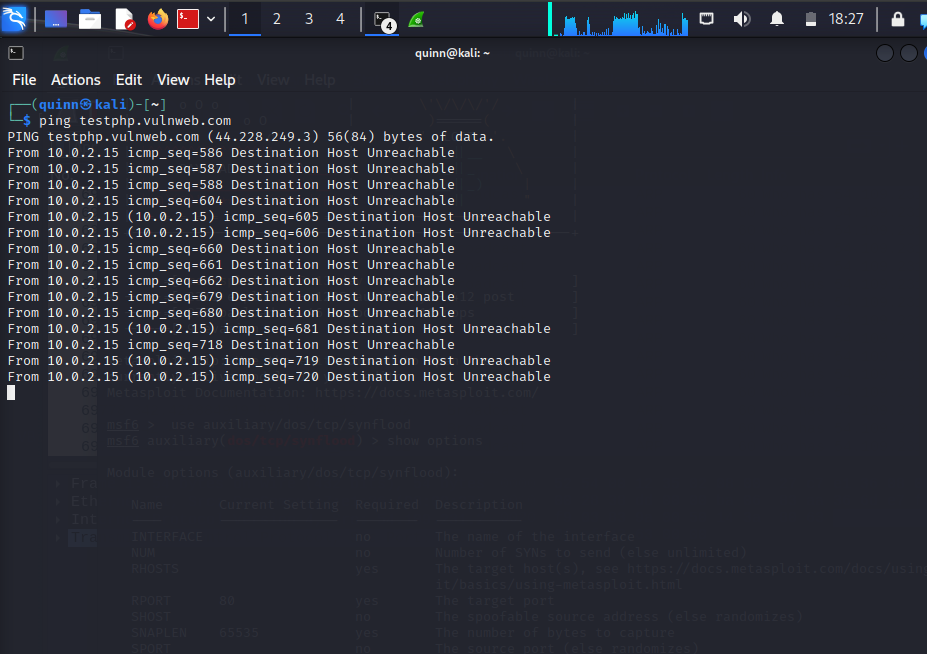
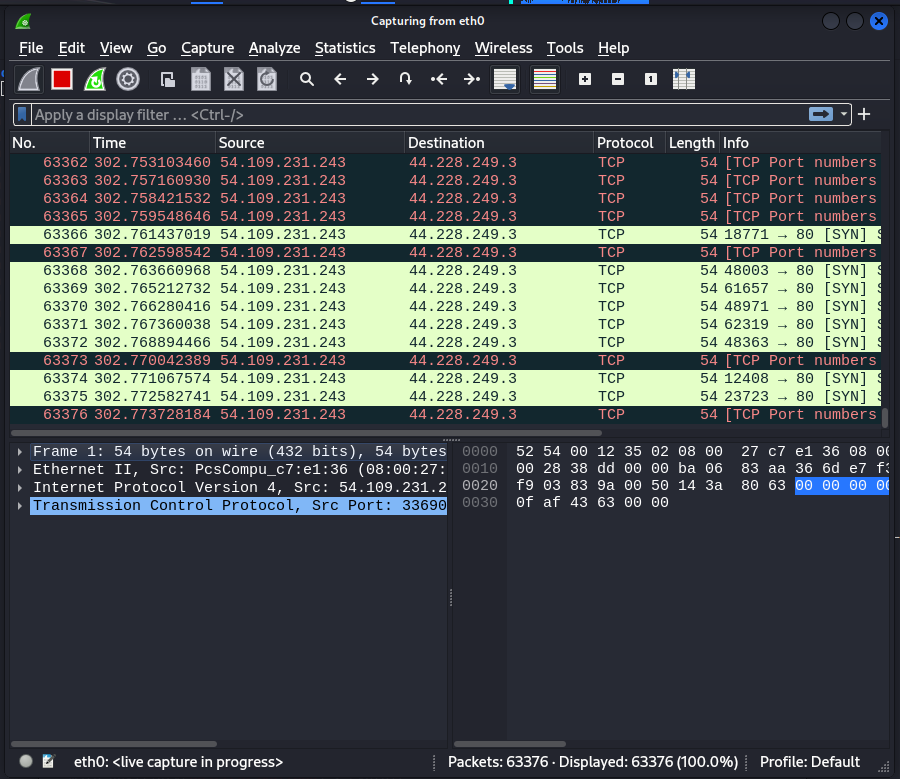
As part of my ongoing exploration of cybersecurity, I recently participated in a hands-on activity focused on understanding and executing a SYN flooding attack, a type of Denial of Service (DDoS) attack. This activity provided me with a practical understanding of how DDoS attacks exploit the normal TCP three-way handshake to consume resources on a targeted server and render it unresponsive.
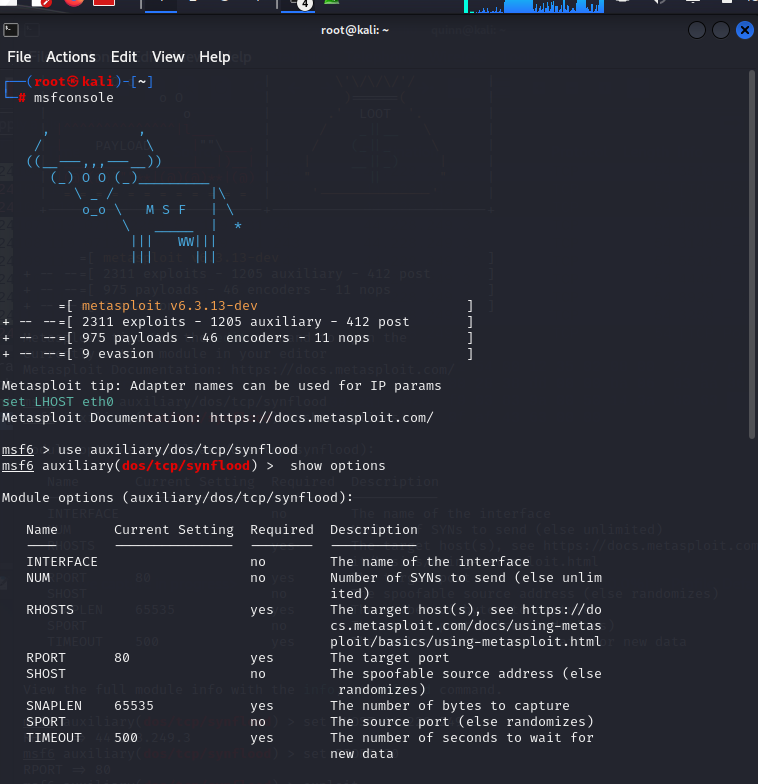
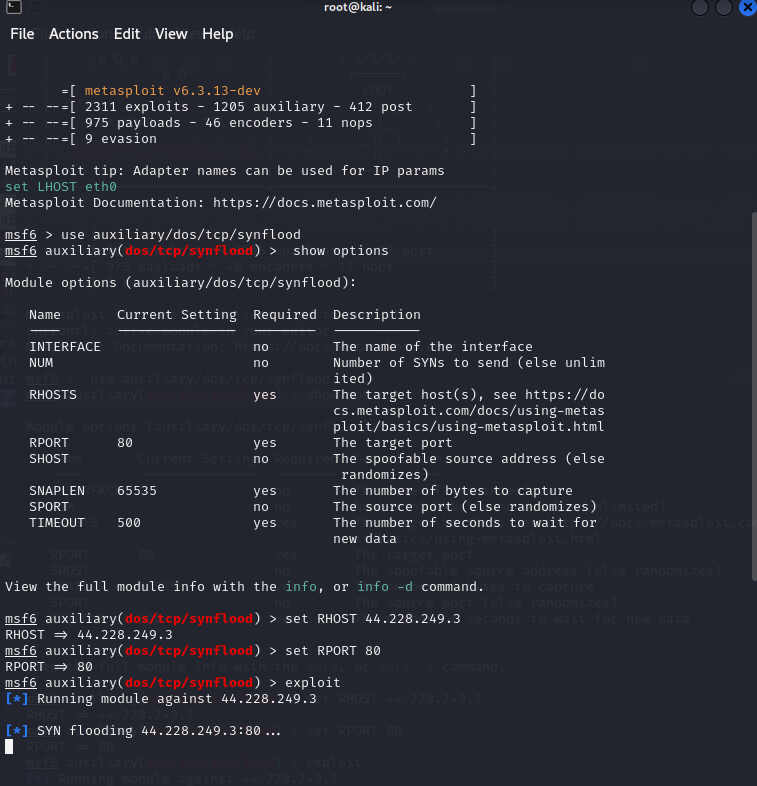
The activity involved using Metasploit, a powerful penetration testing tool, to simulate a SYN flooding attack. I started by launching Metasploit in the terminal and selecting the auxiliary "auxiliary/dos/TCP/synflood". This provided me with a range of options that I could set to execute the attack.
The two main options I needed to set were RHOST and RPORT, which represent the target IP address and the target port address, respectively. I set these options according to the details of the target system.
The essence of the SYN flooding attack lies in sending a large number of SYN packets to all available ports on the victim server, often using a fake IP address. The server, unaware of the attack, responds to each attempt with an SYN-ACK packet from all open ports. The malicious client either does not send the expected ACK, or—if the IP address is spoofed—never receives the SYN-ACK in the first place. This leaves an increasingly large number of connections half-open, eventually leading to denial of service to legitimate clients and potential malfunction or crash of the server.
Reflecting on this activity, I gained a deeper understanding of the mechanisms behind DDoS attacks and the potential damage they can cause. This practical experience has enhanced my technical skills and understanding of network vulnerabilities and how to exploit them.
In conclusion, this DDoS activity was a valuable learning experience. It not only reinforced my theoretical knowledge but also provided practical skills that will be beneficial in my future endeavors in the field of cybersecurity. I look forward to further exploring this fascinating area and applying these skills in real-world scenarios.
Activity-4:Digitalization
Fully Digital Enterprises
Fully digital enterprises are becoming increasingly common in the digital economy. According to Wei et al. (2019), a fully digital enterprise relies on digital technologies for all aspects of its operations, from customer interactions to supply chain management. This includes the use of technologies like cloud computing, big data analytics, and the Internet of Things (IoT). While these technologies can offer many benefits in terms of efficiency and cost savings, they also present several cybersecurity challenges.
One of the main cybersecurity challenges associated with fully digital enterprises is the increased risk of cyber attacks. As more and more of the enterprise's operations are conducted online, the attack surface for cybercriminals increases. This can lead to a greater likelihood of data breaches, ransomware attacks, and other types of cyber attacks. In addition, the use of cloud computing and other third-party services can introduce new vulnerabilities that need to be managed.
Another challenge associated with fully digital enterprises is the need to maintain data privacy and compliance with regulations such as GDPR and CCPA. As more data is generated and stored digitally, it becomes increasingly important for organizations to protect this data and ensure that it is only used in accordance with relevant regulations.
Cybersecurity Challenges for SMEs
While fully digital enterprises may face cybersecurity challenges, SMEs looking to become more digital can face even greater challenges. As Spremic and Simunic (2018) point out, SMEs often have limited budgets for cybersecurity and may not have the same level of access to security technologies and expertise as larger organizations. This can make it more difficult to manage the cybersecurity risks associated with becoming a digital enterprise.
To address these challenges, SMEs can take a variety of approaches. For example, they can partner with managed security service providers (MSSPs) to outsource some of their cybersecurity needs. They can also adopt a risk-based approach to cybersecurity, focusing on the most critical assets and vulnerabilities first. Finally, they can invest in cybersecurity training for their employees to ensure that everyone is aware of best practices and the risks associated with digital technologies.
Energy Crisis and Cybersecurity
The global energy crisis experienced in 2022 has brought new attention to the potential cybersecurity risks associated with the digital economy. As organizations look for ways to reduce their energy consumption, they may turn to technologies like edge computing and the use of renewable energy sources. While these technologies can offer environmental benefits, they may also introduce new cybersecurity risks that need to be managed.
For example, edge computing involves processing data closer to the source, which can increase the attack surface for cybercriminals. Renewable energy sources, such as solar and wind power, may also introduce new vulnerabilities, such as physical attacks on power generation infrastructure.
To address these risks, organizations can take a proactive approach to cybersecurity. This may involve implementing new security measures, such as encryption and multi-factor authentication, to protect against cyber attacks. It may also involve conducting regular risk assessments and updating security policies and procedures as needed to ensure that they remain relevant and effective.
Conclusion
In conclusion, the cybersecurity implications of the digital economy are complex and multifaceted. Fully digital enterprises and SMEs looking to become more digital face different challenges, but both need to take a proactive approach to cybersecurity to mitigate the risks associated with cyber attacks, data breaches, and other security challenges. With the global energy crisis bringing new attention to the potential cybersecurity risks associated with digital technologies, it is more important than ever for organizations to invest in cybersecurity and take steps to manage these risks effectively.
Activity-5:IEEE
The Open Web Application Security Project (OWASP) and the Institute of Electrical and Electronics Engineers (IEEE) are two prominent organizations that provide guidance on cybersecurity vulnerabilities. While both organizations produce lists of the top 10 cybersecurity vulnerabilities, there are some differences between the two lists.
The OWASP Top 10 is a well-known list of the most critical web application security risks. The OWASP Top 10 is updated every few years to reflect changes in the threat landscape. The most recent version of the OWASP Top 10 was released in 2021, and it includes the following vulnerabilities: injection, broken authentication and session management, sensitive data exposure, XML external entities (XXE), broken access control, security misconfigurations, cross-site scripting (XSS), insecure deserialization, using components with known vulnerabilities, and insufficient logging and monitoring (OWASP, 2021).
In contrast, the IEEE Center for Secure Design released their Top 10 Security Design Flaws in 2021. This list focuses on design-level issues that can lead to security vulnerabilities. The IEEE Top 10 includes the following vulnerabilities: insecure data storage, insecure communications, inadequate error handling and logging, security decisions via untrusted inputs, insufficient authentication/authorization, insecure time and state, code quality, resource management, cryptography, and compliance (IEEE, 2021).
One of the main differences between the two lists is their focus. The OWASP Top 10 focuses on web application security risks, while the IEEE Top 10 focuses on design-level issues that can lead to security vulnerabilities. Another difference is that the OWASP Top 10 includes vulnerabilities such as injection and XSS, which are specific to web applications, while the IEEE Top 10 includes vulnerabilities such as code quality and resource management, which are more general in nature.
In conclusion, both the OWASP Top 10 and the IEEE Top 10 provide valuable guidance on cybersecurity vulnerabilities. While there are some differences between the two lists, both can help organizations prioritize their cybersecurity efforts and mitigate the risks associated with these vulnerabilities.
References:
Open Web Application Security Project. (2021). OWASP Top Ten Project. Retrieved from https://owasp.org/Top10/
IEEE Center for Secure Design. (2021). Top 10 Security Design Flaws. Retrieved from https://www.computer.org/education/best-practices/top-10-security-design-flaws
Activity-6:Solar Winds
The Solar Winds exploit was a highly sophisticated cyber attack that targeted the software supply chain, compromising several high-profile organizations, including US government agencies. The Cyber Kill Chain model provides a useful framework for analyzing cyber attacks and is widely employed by security professionals.
Reconnaissance: The attackers likely conducted extensive reconnaissance to identify potential targets and gather information about the Solar Winds software. To mitigate this phase, organizations can restrict public information about their networks and infrastructure. Employing tools such as search engines and social media monitoring can help detect potential leaks of sensitive information.
Weaponization: Once the attackers identified their targets, they developed an exploit to target a vulnerability in the Solar Winds software. Mitigations for this phase include promptly implementing security patches and updates. Organizations should regularly update their software to address known vulnerabilities.
Delivery: The attackers delivered the exploit to their targets through various delivery mechanisms such as email and websites. Mitigations for this phase include monitoring email, web, and other delivery channels for malicious content. Implementing email filtering and web proxy servers can help prevent the delivery of malicious content.
Exploitation: Once the exploit was delivered, the attackers used it to gain unauthorized access to the target network. Mitigations for this phase include implementing strong access control policies, such as the principle of least privilege. Regular security awareness training and conducting penetration testing can help identify and patch vulnerabilities in the network.
Installation: After gaining access to the target network, the attackers installed malware to maintain persistence. Mitigations for this phase include implementing application whitelisting and disabling unnecessary software. Antivirus and endpoint protection tools should be employed to detect and prevent malware installation.
Command and Control (C2): The attackers established communication with their command-and-control server to receive instructions and exfiltrate data. Mitigations for this phase include implementing network segmentation and restricting inbound/outbound traffic. Intrusion detection and prevention systems can help detect and prevent C2 traffic.
Actions on Objective: Once the attackers gained access to the target network and established C2 communication, they performed malicious activities such as data exfiltration. Mitigations for this phase include implementing data loss prevention measures and maintaining robust backup and recovery processes. Security information and event management (SIEM) systems can aid in detecting and responding to malicious activities.
| Phase | Description | Mitigations | Tools |
|---|---|---|---|
| Reconnaissance | Gathering information about the target. | Restrict public information about the network and its infrastructure. | Search engines and social media tools. |
| Weaponization | Creating an exploit. | Implement security patches and updates regularly. | Exploit development frameworks such as Metasploit. |
| Delivery | Delivering the exploit. | Monitor email, web, and other delivery mechanisms for malicious content. | Email filtering and web proxy servers. |
| Exploitation | Exploiting the vulnerability. | Implement least privilege access control policies and regular security awareness training. | Penetration testing tools such as Nessus and OpenVAS. |
| Installation | Installing malware on the target. | Implement application whitelisting and disable unnecessary software. | Antivirus and endpoint protection tools. |
| Command and Control (C2) | Establishing communication with the attacker. | Implement network segmentation and restrict inbound/outbound traffic. | Intrusion detection and prevention systems. |
| Actions on Objective | Performing malicious activities on the target. | Implement data loss prevention and backup and recovery processes. | Security information and event management (SIEM) systems. |
There are no phases that cannot be identified using the Cyber Kill Chain model, as the model covers the entire lifecycle of a cyber-attack from initial reconnaissance to final exfiltration of data.
Possible mitigations for each phase include implementing security patches and updates, monitoring delivery mechanisms for malicious content, implementing least privilege access control policies, implementing application whitelisting, and restricting inbound/outbound traffic.
Tools that could be utilized in each phase include search engines and social media tools for reconnaissance, exploit development frameworks such as Metasploit for weaponization, email filtering and web proxy servers for delivery, penetration testing tools such as Nessus and OpenVAS for exploitation, antivirus and endpoint protection tools for installation, intrusion detection and prevention systems for C2, and SIEM systems for actions on objective.
Slide part
The Solar Winds Exploit Using the Cyber Kill Chain
Certainly, here's a table analyzing the SolarWinds exploit using the Cyber Kill Chain model:
| Phase of Cyber Kill Chain | Description | Relation to SolarWinds Exploit |
|---|---|---|
| Reconnaissance | The attacker gathers information about the target organization, such as its network architecture, security systems, and potential vulnerabilities. | APT29 conducted extensive reconnaissance before launching the SolarWinds exploit, studying SolarWinds' network architecture and identifying weaknesses that could be exploited. |
| Weaponization | The attacker creates a malicious payload, such as a virus or Trojan, and attaches it to a delivery mechanism. | APT29 inserted malicious code into an update of SolarWinds' Orion product and used it as a delivery mechanism to distribute the malware to thousands of SolarWinds customers. |
| Delivery | The attacker sends the malicious payload to the target, usually via email or a compromised website. | SolarWinds' Orion update was delivered to thousands of SolarWinds customers via their software update process. |
| Exploitation | The attacker exploits a vulnerability in the target's systems to gain access and execute the malicious code. | APT29 exploited a vulnerability in SolarWinds' update process, allowing them to execute the malicious code and gain access to targeted systems. |
| Installation | The attacker installs the malware on the target system, usually with escalated privileges. | Once APT29 gained access to a system, they installed the malware with elevated privileges, allowing them to maintain persistence and evade detection. |
| Command and Control | The attacker establishes communication channels with the malware on the target system, allowing them to remotely control and monitor the compromised system. | APT29 established command and control channels with the malware on compromised systems, allowing them to remotely control and monitor their activities. |
| Actions on Objectives | The attacker carries out their intended malicious activities, such as stealing data or causing damage to the target system. | APT29's objectives in the SolarWinds exploit are not fully known, but it is believed that they stole sensitive information from a variety of targeted organizations. |
In the case of the SolarWinds exploit, APT29 followed each phase of the Cyber Kill Chain model to successfully carry out the attack. They conducted extensive reconnaissance to identify potential targets and weaknesses in SolarWinds' network architecture, then used a weaponized delivery mechanism to distribute the malware to thousands of SolarWinds customers. Once the malicious code was executed on a targeted system, APT29 installed it with elevated privileges to maintain persistence and evade detection. They established command and control channels with the malware on compromised systems, allowing them to remotely control and monitor their activities. Finally, APT29 carried out their intended malicious activities, which included stealing sensitive information from targeted organizations. By understanding each phase of the Cyber Kill Chain model and how it relates to the SolarWinds exploit, organizations can better protect themselves from similar attacks by implementing appropriate security measures and responding quickly when an attack is detected.
Possible mitigations for each phase:
Implementing security patches and updates, monitoring delivery mechanisms for malicious content, implementing least privilege access control policies, implementing application whitelisting, and restricting inbound/outbound traffic can help mitigate each phase of the Cyber Kill Chain.
Tools that could be utilized in each phase include search engines and social media tools for reconnaissance, exploit development frameworks such as Metasploit for weaponization, email filtering and web proxy servers for delivery, penetration testing tools such as Nessus and OpenVAS for exploitation, antivirus and endpoint protection tools for installation, intrusion detection and prevention systems for C2, and SIEM systems for actions on objective.
List of tools for each phase:
Here's a list of tools that could be utilized in each phase of the Cyber Kill Chain:
Reconnaissance:
- Port scanners (e.g. Nmap) to identify open ports and services
- Social media monitoring tools (e.g. Hootsuite) to identify publicly available information
- Whois lookup tools (e.g. WHOIS) to identify information about domain names and IP addresses
Weaponization:
- Anti-virus and anti-malware software (e.g. Norton, McAfee) to detect and prevent malicious payloads from being delivered
- Email filters (e.g. Proofpoint, Barracuda) to prevent the delivery of malicious attachments or links
- Sandboxing tools (e.g. Cuckoo Sandbox) to test suspicious files in a safe environment before execution
Delivery:
- Spam filters (e.g. SpamAssassin, Exchange Online Protection) to prevent delivery of phishing emails and spam
- DNS filtering (e.g. OpenDNS) to block access to known malicious domains
- Web content filtering (e.g. Symantec Web Security Service, Cisco Umbrella) to block access to malicious websites
Exploitation:
- Vulnerability scanners (e.g. Nessus, OpenVAS) to identify and prioritize vulnerabilities
- Intrusion detection/prevention systems (e.g. Snort, Suricata) to detect and prevent exploitation attempts
- Security information and event management (SIEM) tools (e.g. Splunk, LogRhythm) to monitor and analyze network activity for signs of exploitation
Installation:
- Application control solutions (e.g. McAfee Application Control, Microsoft AppLocker) to restrict the execution of unauthorized software
- Endpoint protection solutions (e.g. Carbon Black, Crowdstrike) to detect and prevent installation of malicious code
- Software restriction policies (e.g. Windows Software Restriction Policies) to restrict the execution of unauthorized software
Command and Control:
- Network security solutions (e.g. FireEye Network Security, Palo Alto Networks) to detect and prevent communication with known command and control servers
- Security analytics tools (e.g. RSA NetWitness, IBM QRadar) to monitor and analyze network activity for signs of command and control activity
- Domain name system (DNS) security solutions (e.g. Infoblox, BlueCat) to block communication with known malicious domains
Actions on Objectives:
- Data loss prevention solutions (e.g. Symantec DLP, McAfee DLP) to prevent the exfiltration of sensitive information
- Network segmentation tools (e.g. Cisco TrustSec, VMware NSX) to limit the impact of successful attacks
- Incident response and management solutions (e.g. IBM Resilient, ServiceNow IRM) to manage and respond to security incidents
Using these tools and implementing the suggested mitigations can significantly enhance an organization's ability to detect and prevent cyber attacks. It's important to note that no single solution or tool can provide complete protection, but by adopting a proactive and layered approach to security, organizations can reduce their risk and respond effectively to threats.
Activity-7:Comprehensive Cybersecurity Threat Analysis and Mitigation
Hands-On Cybersecurity: A Journey Through Practical Learning
In my recent academic journey, I delved into the complex and fascinating world of cybersecurity, gaining invaluable skills and insights through a series of hands-on lab activities.
One of the first activities involved assessing the impact of malware. For this, I utilized a variety of cybersecurity software and platforms to analyze and understand the behavior of different malware samples. This activity provided me with a deep understanding of the threats posed by malware and the importance of robust cybersecurity measures.
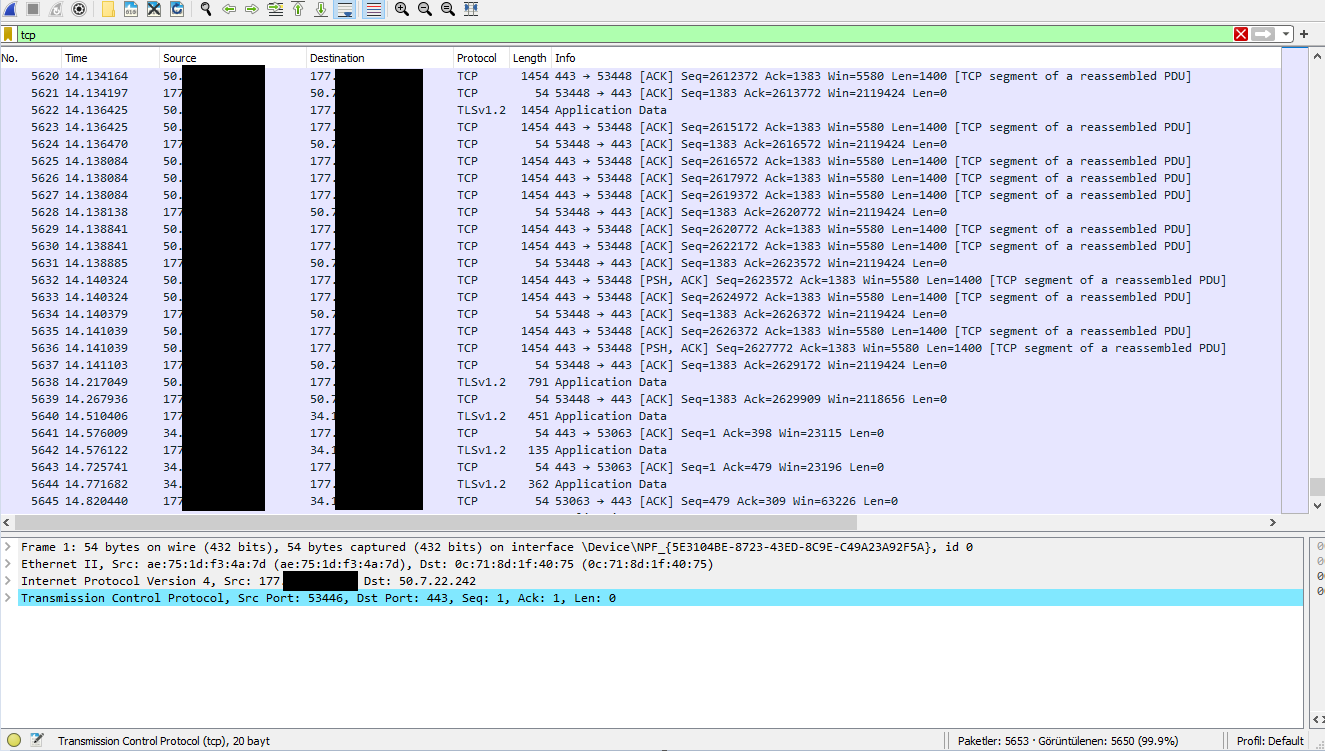
Next, I used Wireshark, a widely used network protocol analyzer, to analyze network protocols. This involved capturing and interacting with live network data, filtering for specific information, and identifying potential anomalies that could indicate a security breach. This hands-on experience with Wireshark significantly enhanced my practical skills in network analysis and threat detection.
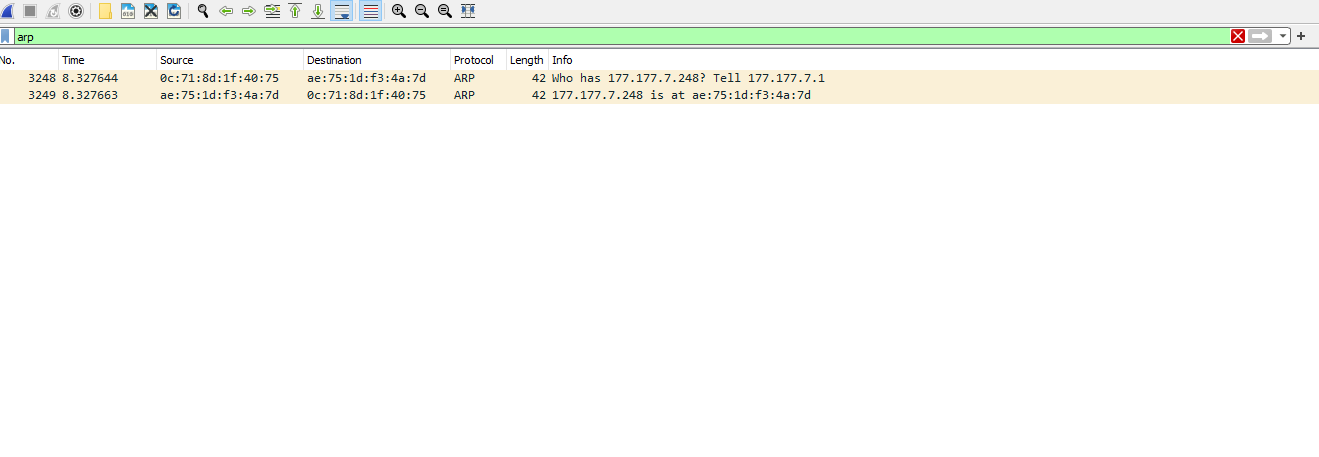
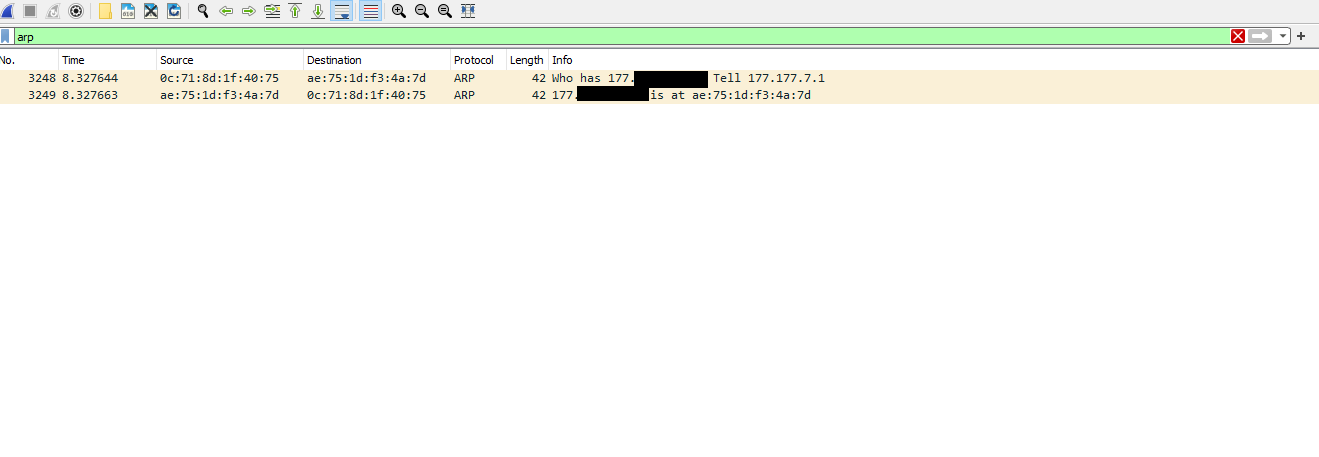
In another activity, I confirmed a spoofing attack using Wireshark. By inspecting individual data packets and their source and destination addresses, I was able to identify and confirm a spoofing attack, demonstrating my ability to apply theoretical knowledge to real-world scenarios.
I also analyzed a capture file using Wireshark to identify potential attacks. This activity required a deep understanding of network protocols and potential vulnerabilities, as well as a keen eye for detail. Successfully identifying attacks in a capture file further demonstrated my proficiency in practical cybersecurity skills.
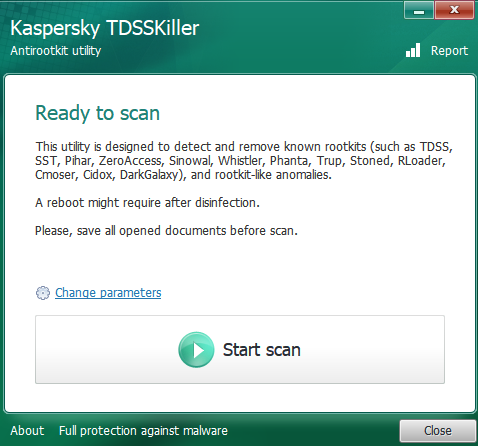
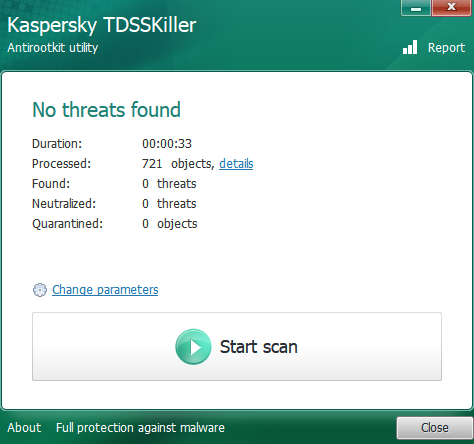
In addition to Wireshark, I used TDSSKiller, a rootkit scanner developed by Kaspersky Lab, to scan for and remove any rootkits on a system. This tool provided me with hands-on experience in dealing with sophisticated malware threats.
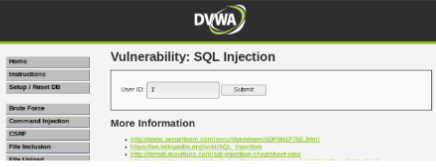
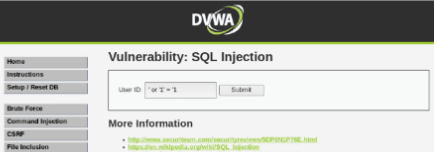
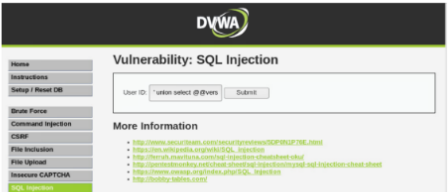
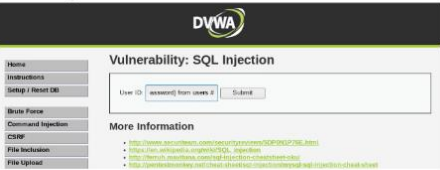
One of the most enlightening activities involved using the Damn Vulnerable Web Application (DVWA) - a PHP/MySQL web application that is intentionally vulnerable. I used this tool to practice my skills in a safe and legal environment, further enhancing my understanding of web application security. One of the key exercises I performed with DVWA was exploiting a website using SQL Injection, a code injection technique used to attack data-driven applications. This activity gave me a practical understanding of how SQL Injection attacks work and how they can be prevented.
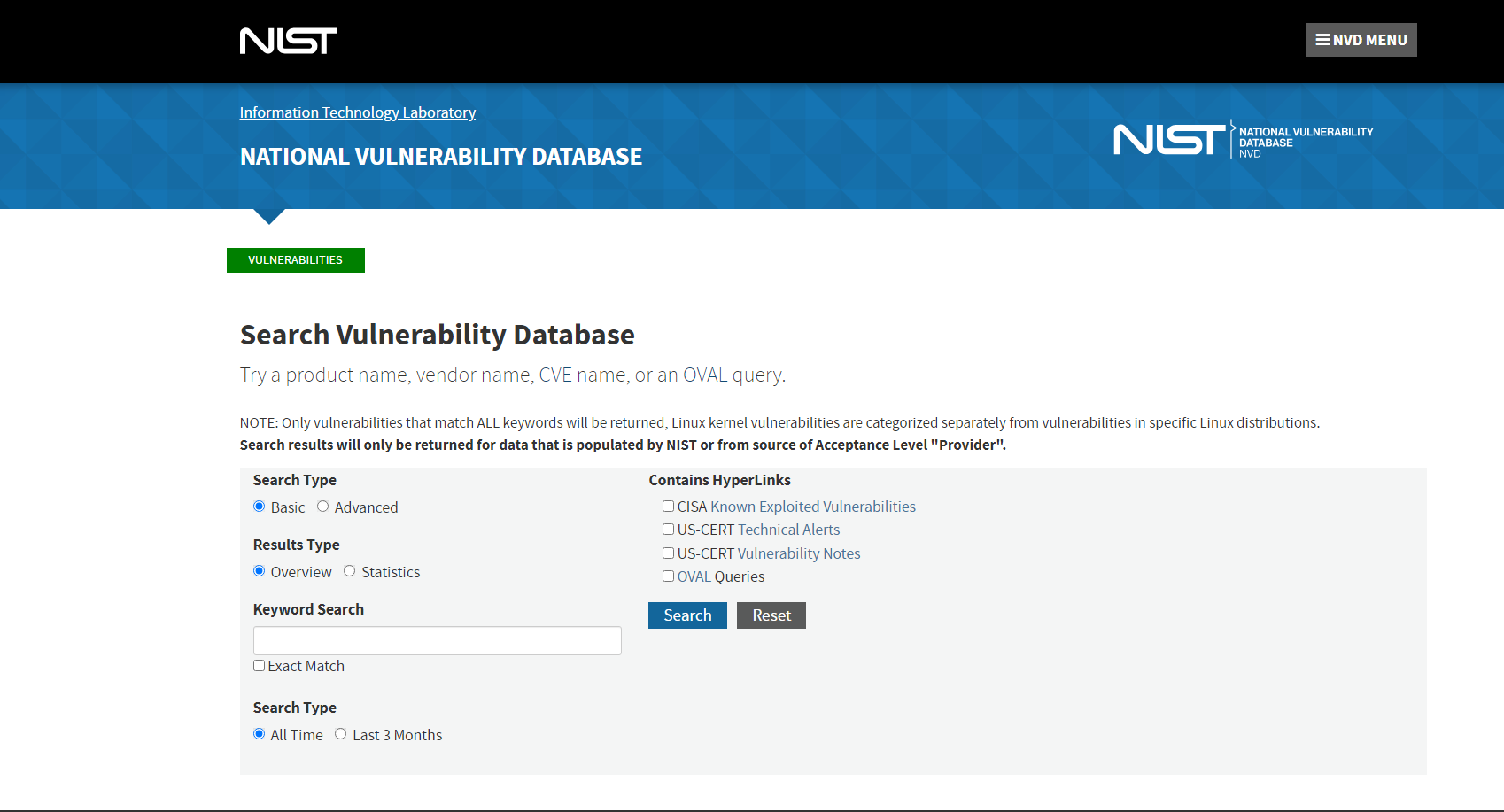
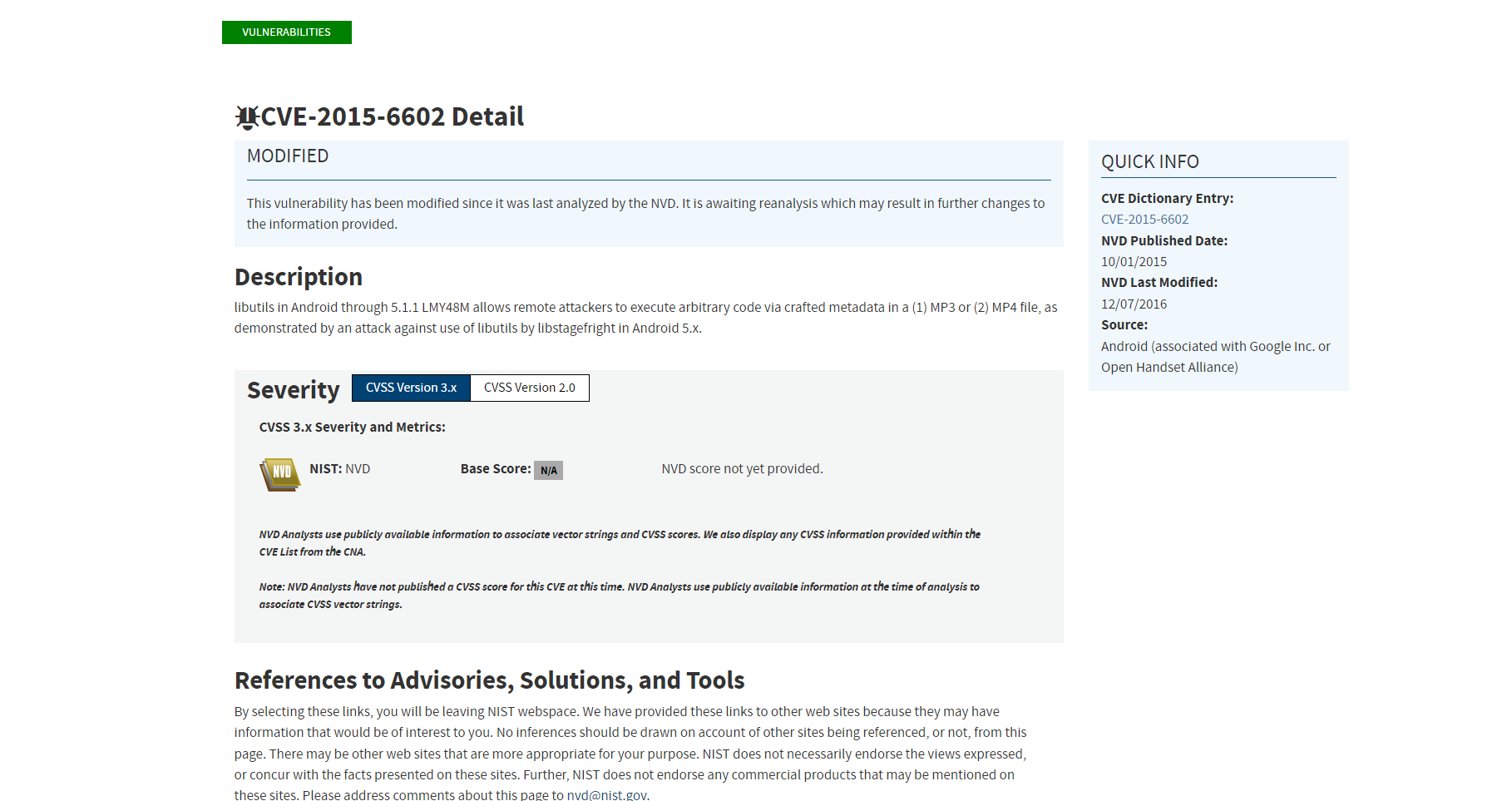
Lastly, I consulted a vulnerability database to understand the various known vulnerabilities that can be exploited by malicious entities. This activity emphasized the importance of staying updated with the latest vulnerabilities and the patches released to fix them.
Each of these activities contributed to my overall understanding of cybersecurity and equipped me with practical skills that will be invaluable in my future endeavors in the field. This hands-on approach to learning has not only enhanced my theoretical knowledge but also prepared me for real-world cybersecurity challenges.
Activity-8:Cyber Security in the Digital Economy
The digital economy, a term coined by Don Tapscott in 1995, refers to new business models, markets, goods, and services based on digital technologies. The integration and simultaneous application of various digital technologies such as cloud computing, mobile technology, sensors, Internet of Things (IoT), big data, cognitive technologies (AI), augmented reality (AR), robotics, additive manufacturing (3D printing), drones, and others have the ability to extract information from physical devices, disseminate it quickly, store it on the cloud, and analyze it instantly. This integration of products, services, and processes has a disruptive impact on established business models.
However, the interconnected capabilities of digital technologies, while bringing many benefits, also introduce a host of new vulnerabilities with far-reaching implications. Cyber security incidents can have a very negative impact on many levels, causing direct financial and other damages, and indirect effects such as legal obligations, lost privacy, stolen identity, regulatory penalties, loss of reputation, and bad public image. Many organizations still do not have sound policies to manage this.
The nature of IT security incidents has changed from isolated attacks on information systems to intentional, targeted, and sophisticated cyber threats at individual, institutional, or even national level. Cyber incidents have a carefully planned 'life cycle', consisting of phases such as 'sniffing', 'exploring', vulnerability analysis, assessment of identified vulnerabilities and preparation of ‘test’ attack, ‘test’ (experiential) cyber attack, analysis of test attack results, 'learning' about security controls which should detect and prevent the attack, cyber attack ‘improvements’, next test attack, and major attack (well prepared) with the specific objective.
The main objective in managing cyber security is to carefully design and apply basic, sophisticated, and smart, but effective and efficient security controls to address common, advanced, and emerging threats to information stored in information systems supported by digital technologies. Cyber security activities should no longer be solely the responsibility of IT departments or assigned individuals (CISOs or similar), but institution-wide efforts with all employees engaged.
A preliminary research on large companies in Croatia related to important or critical national infrastructure revealed that basic protection is efficient, but there are still rooms for improvements in taking a collective ambition towards holistic cyber security governance and applying more advanced controls. The research also revealed that highest executives (C-suite level executives) still assume cyber security is solely the responsibility of IT departments or assigned individuals (CISO and similar). In that light, companies should take a more holistic and collective ambition toward cyber security management. Cyber security should be the responsibility of every employee and even of the people in the ecosystem of the organization.
In conclusion, as digital technologies are strategically aligned with business strategy, the same should be done with cyber security. The more effective basic and advanced controls which are detecting and preventing all cyber threats an organization implement, it is less likely to be exposed to cyber risks, or will be exposed to lower risk level.
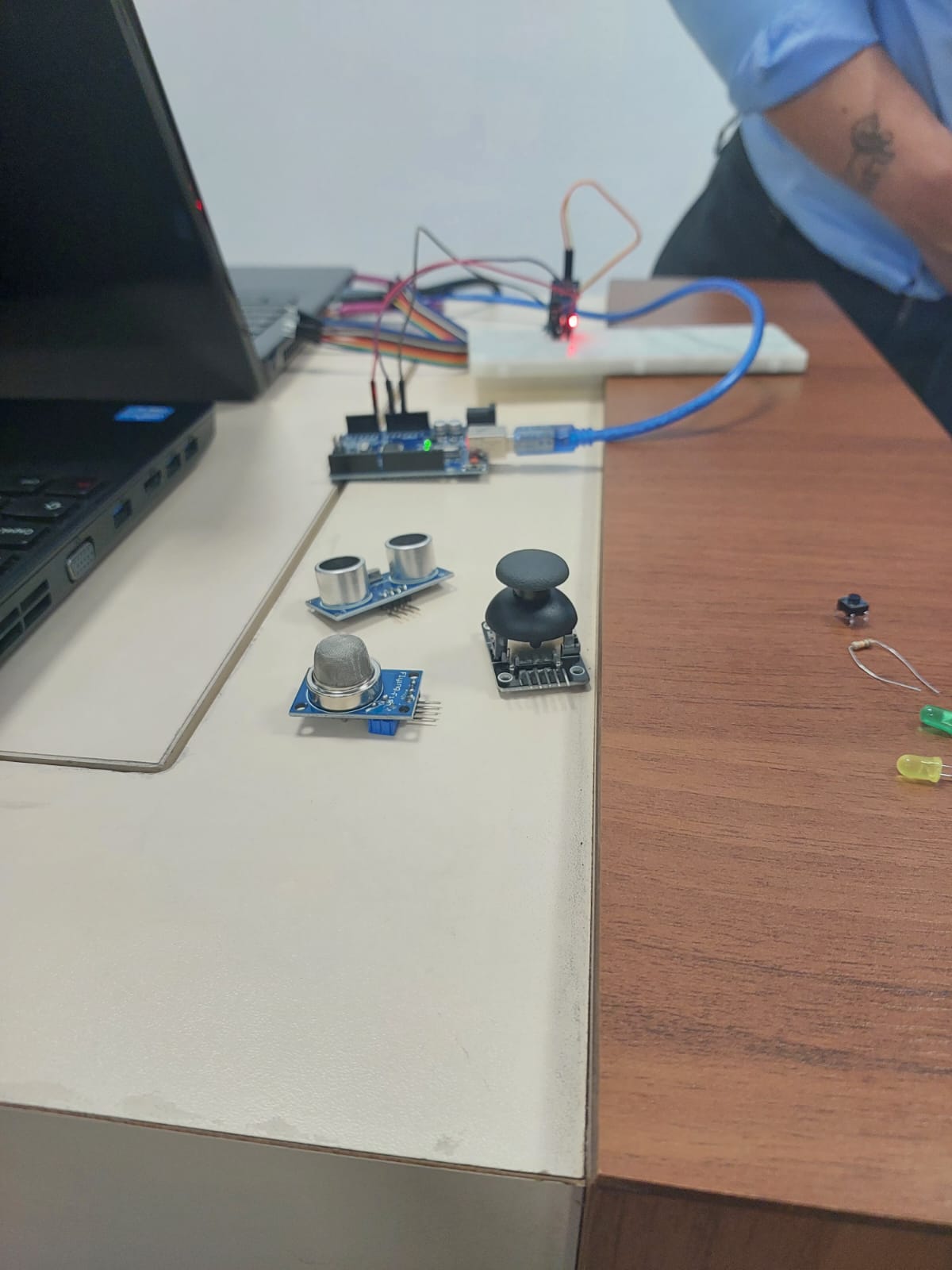
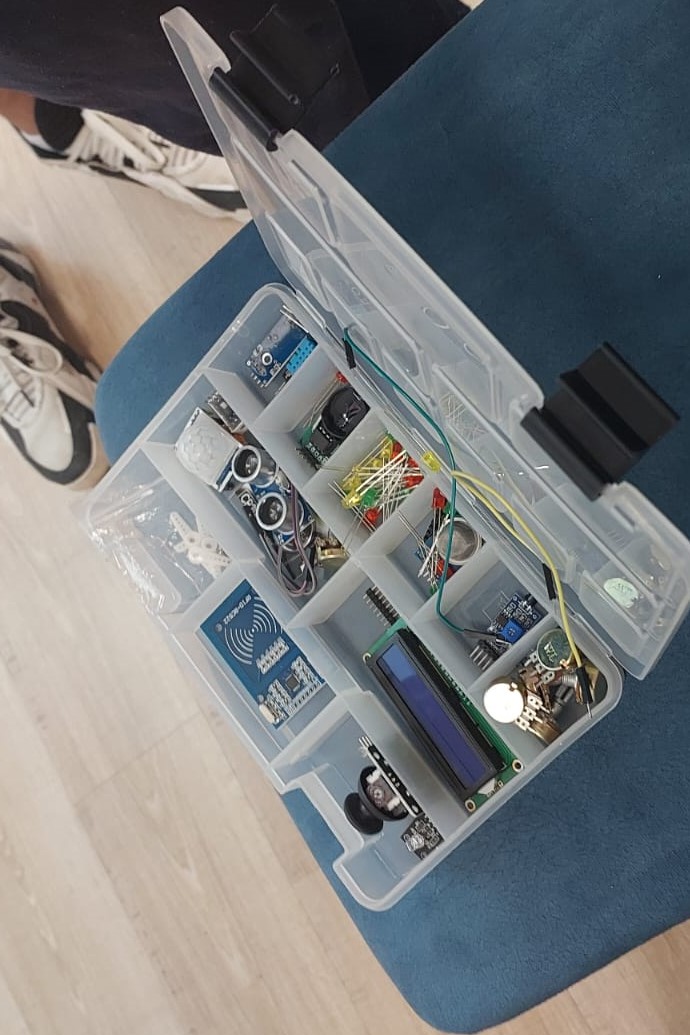
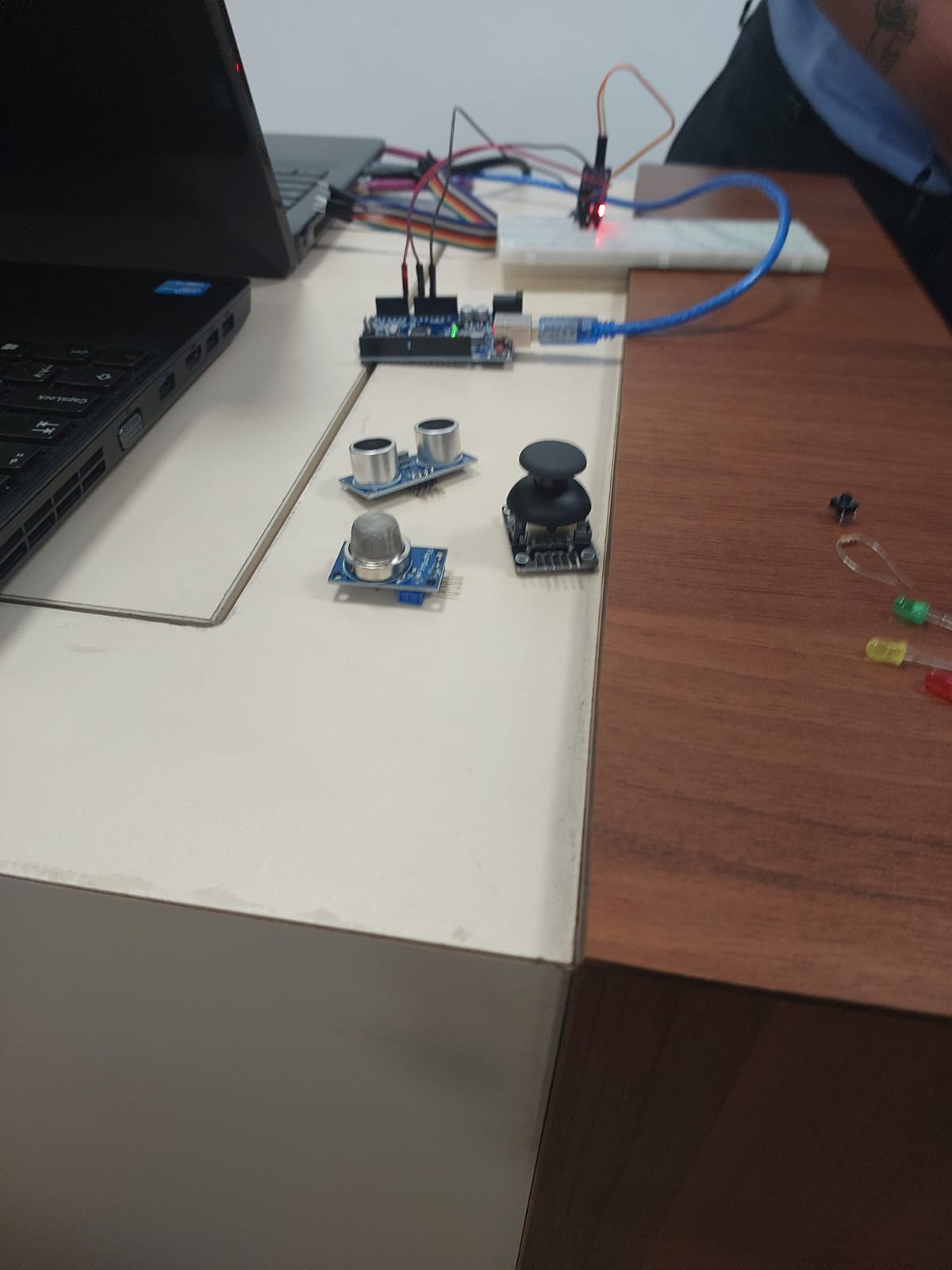
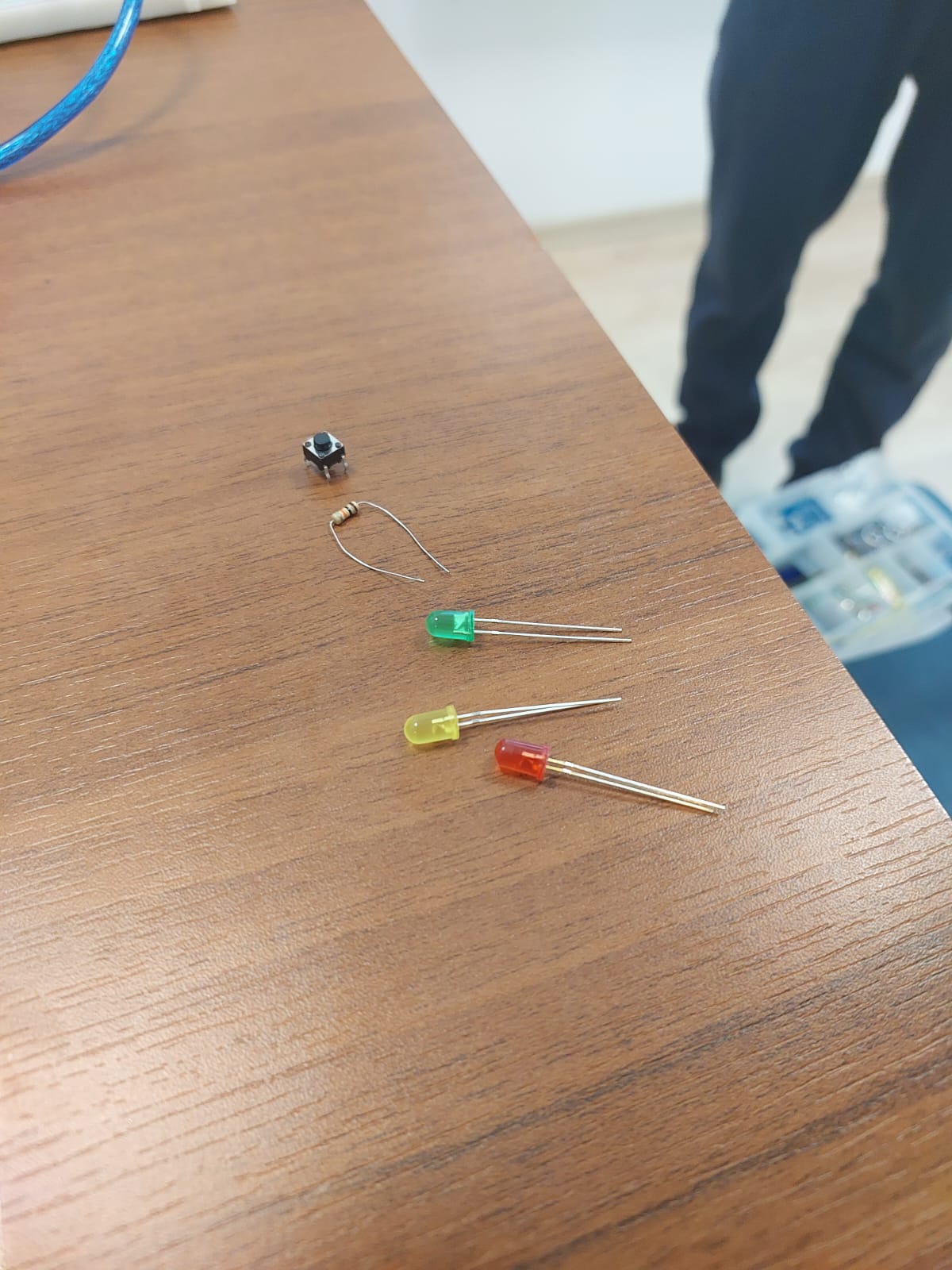
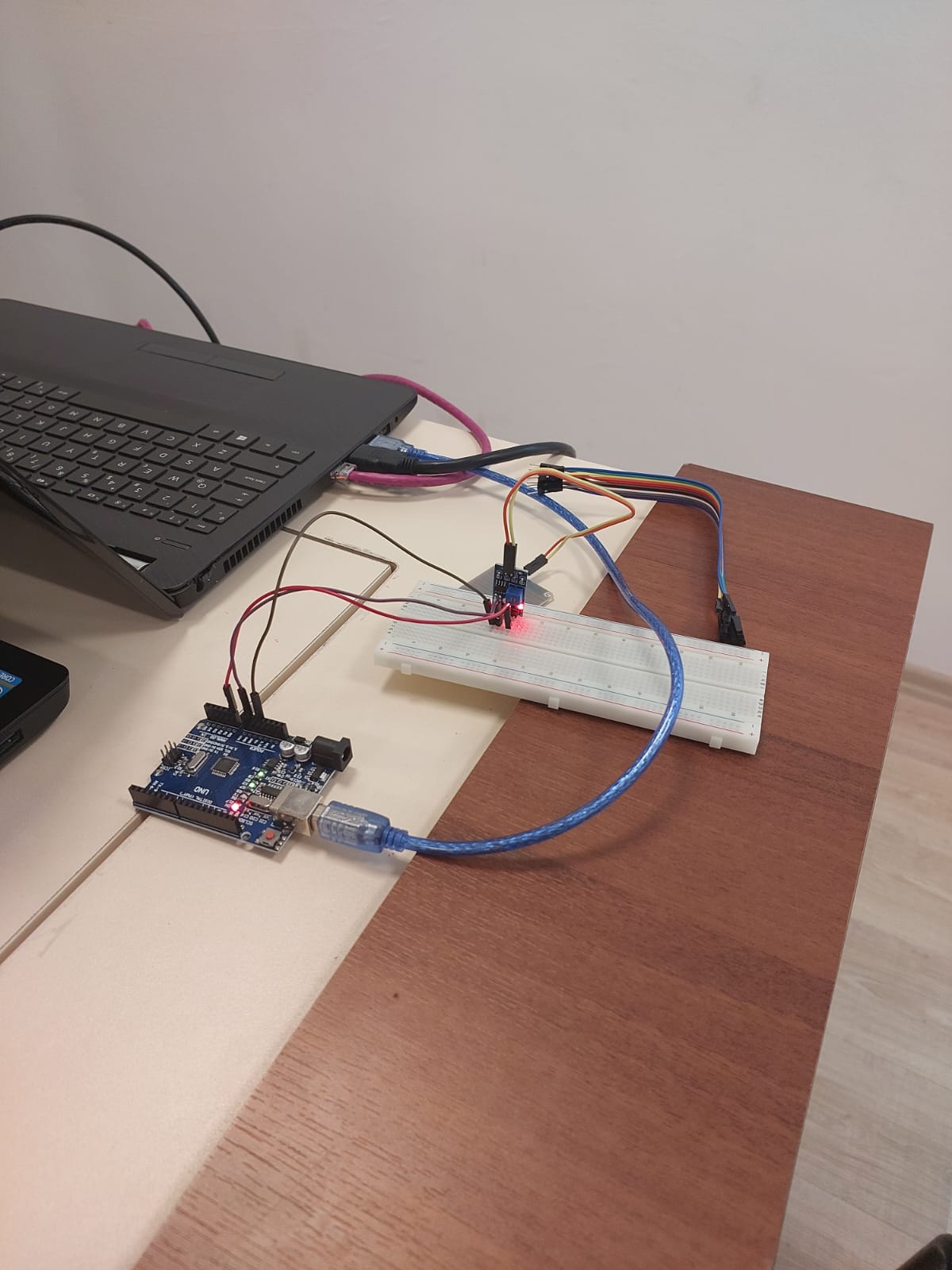
Activity-9:Using IoT to Solve Problems
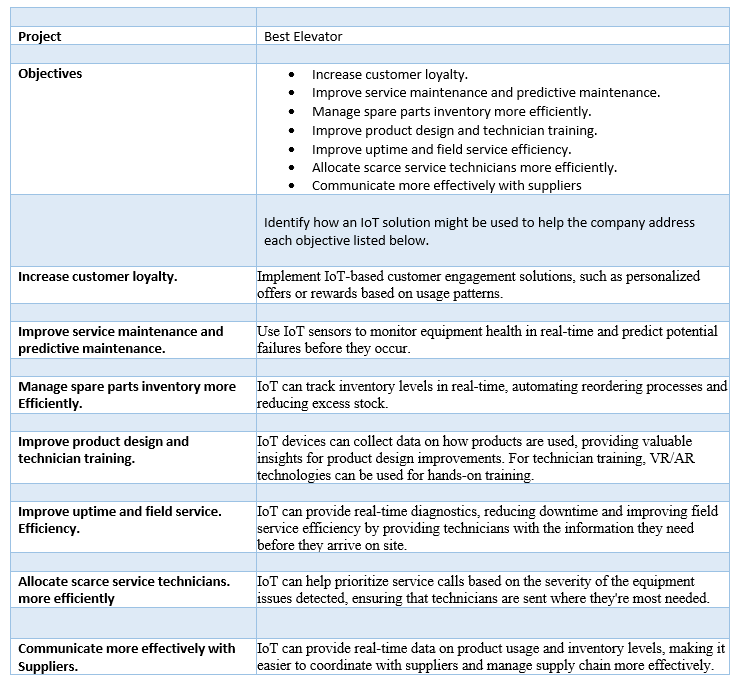
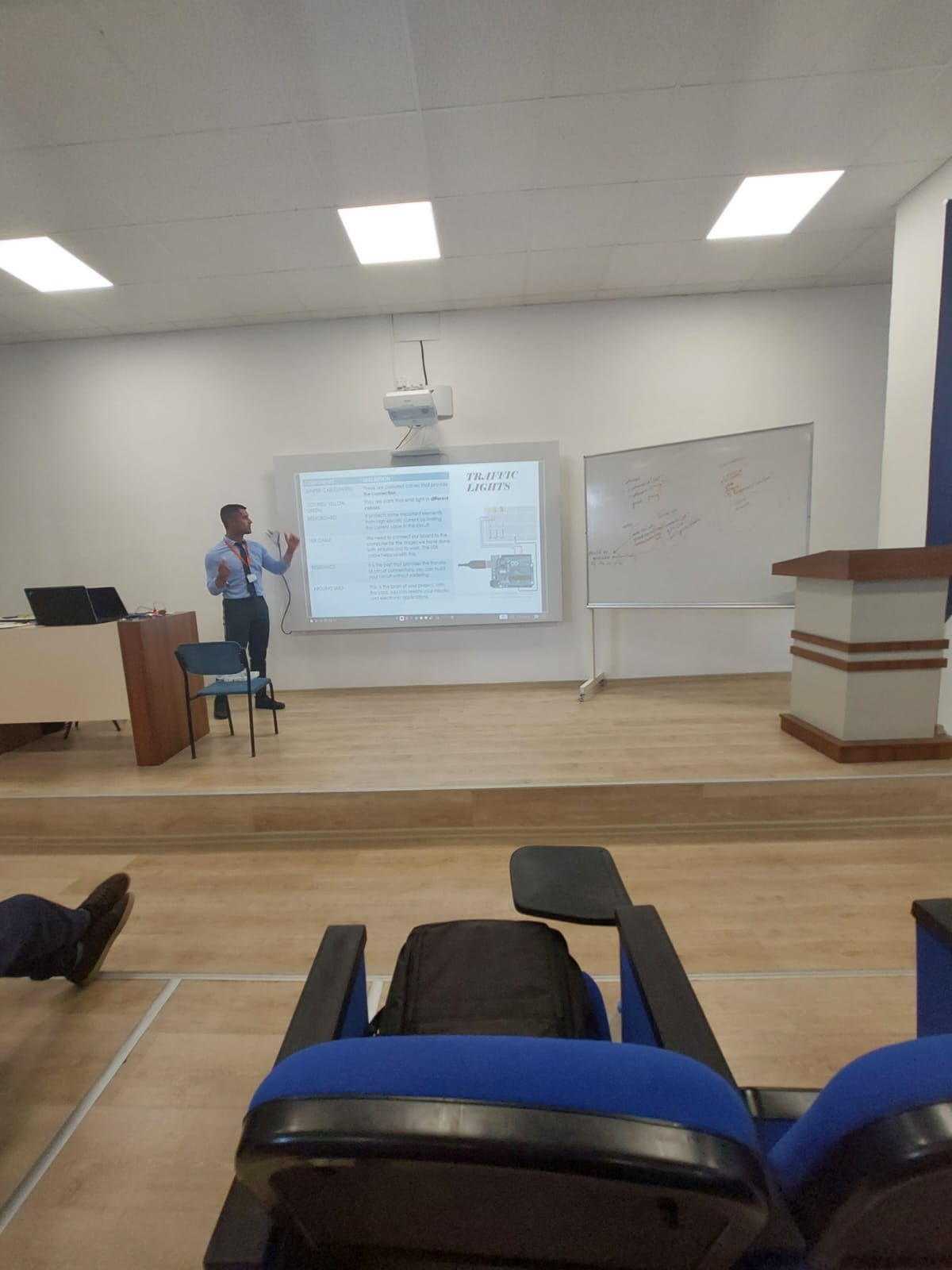
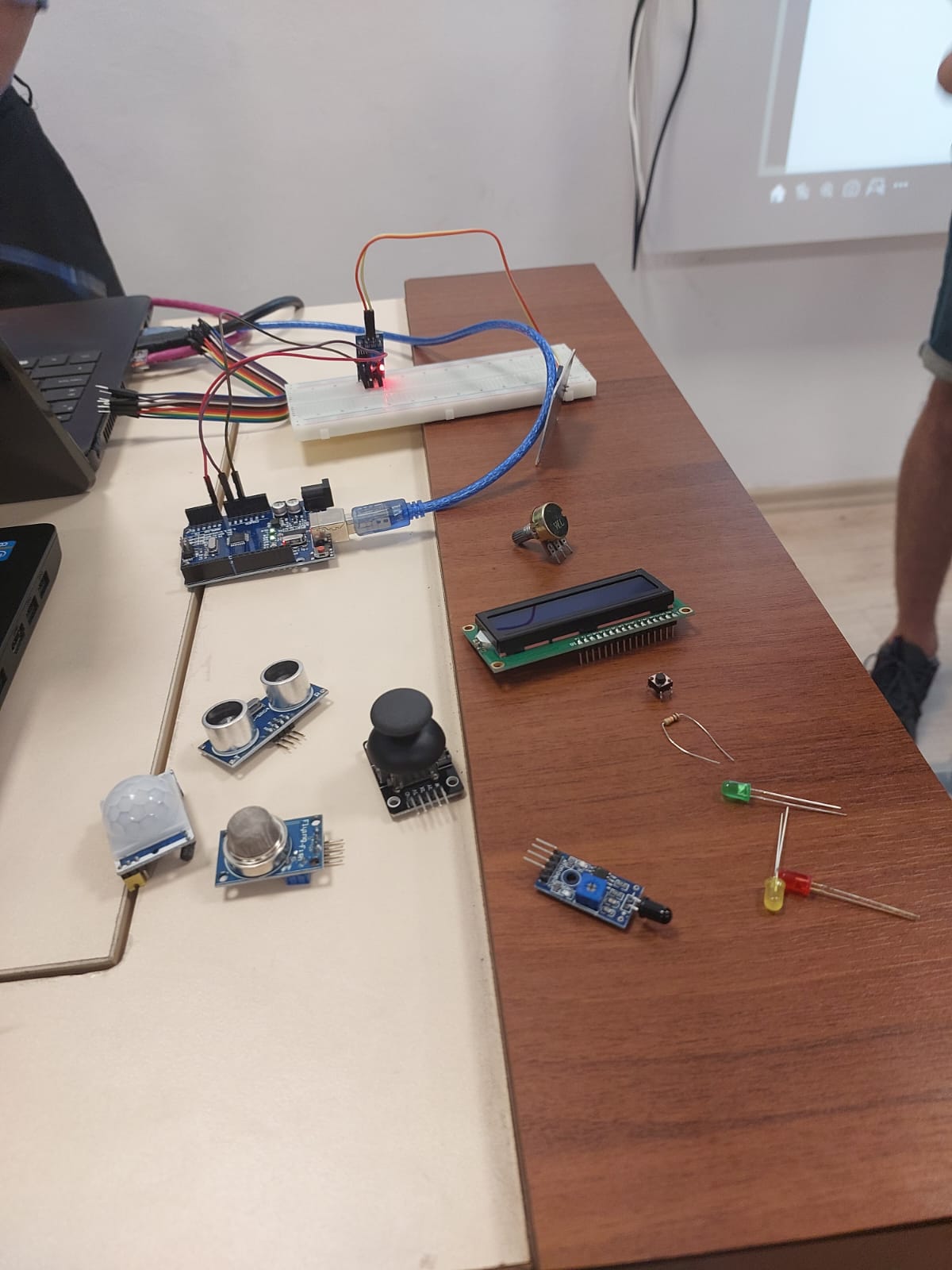
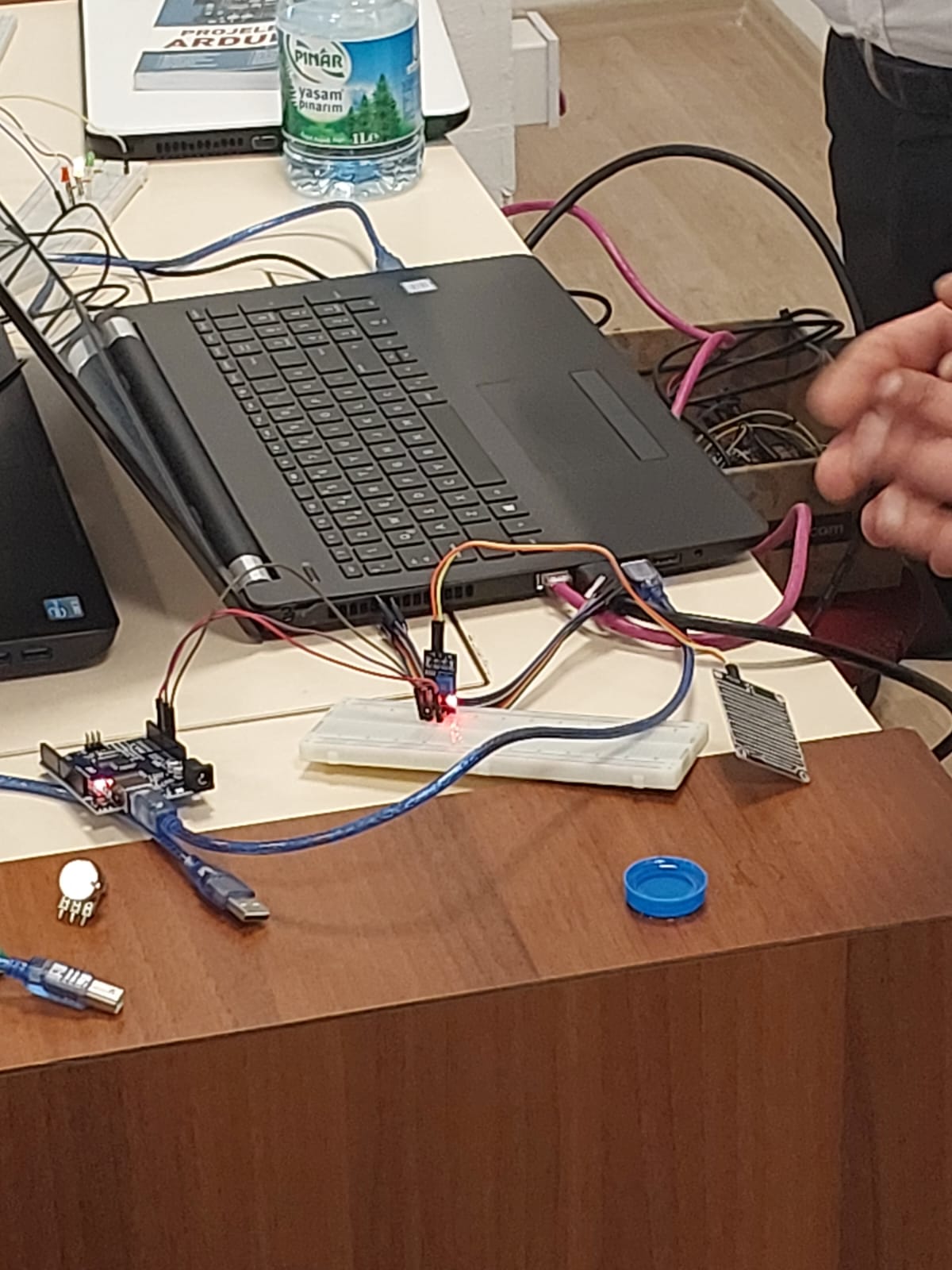
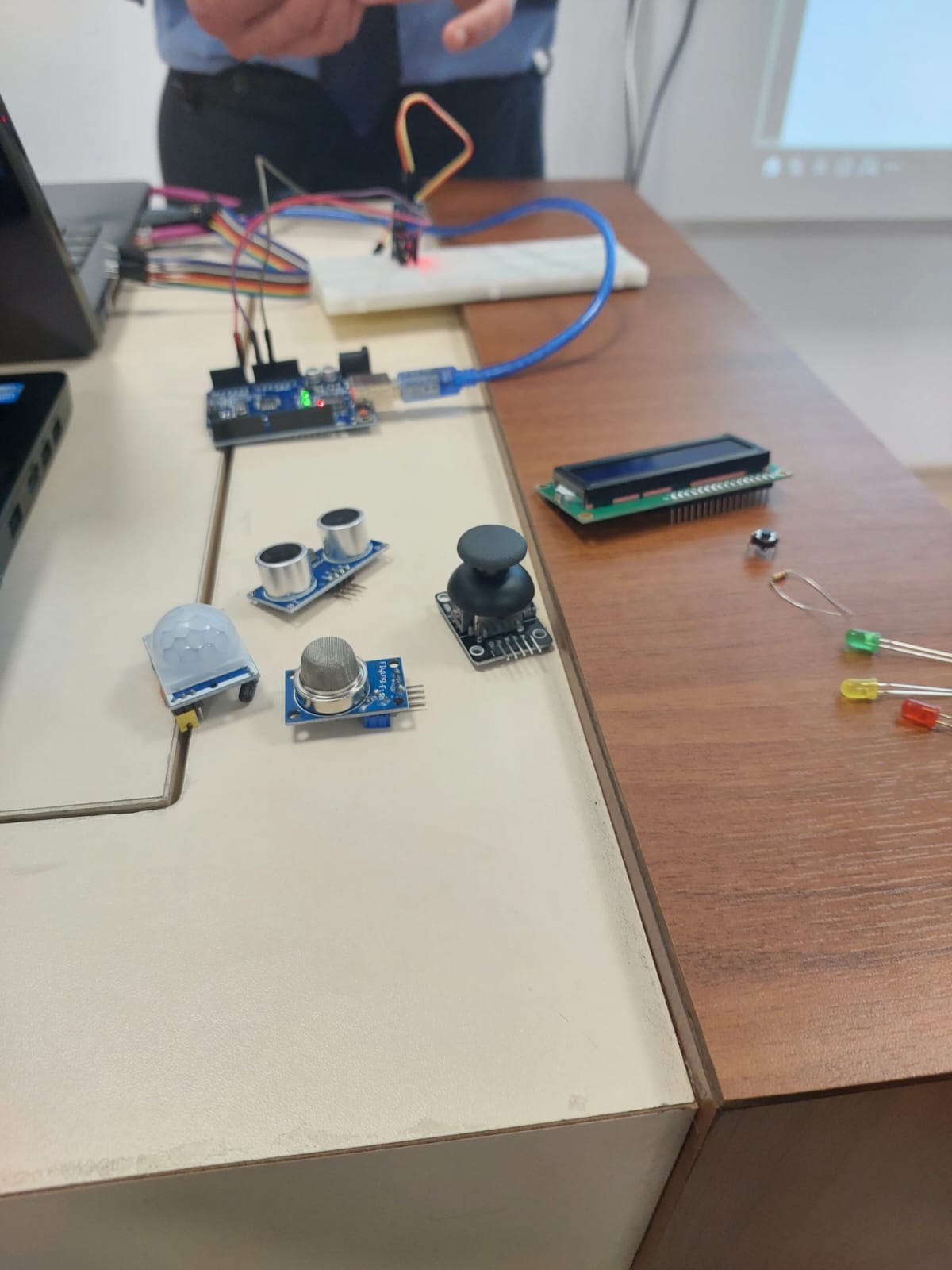
An Insight into IoT and Arduino Programming: A Seminar Review
An Internet of Things (IoT) seminar I recently attended has enriched my understanding of the practical implications of IoT and Arduino programming. The comprehensive seminar was conducted by an experienced presenter with an in-depth understanding of IoT programming, specifically using the Arduino Integrated Development Environment (IDE). This essay aims to encapsulate the learning journey I embarked on throughout this seminar, delving into how IoT works and the intricacies involved in programming IoT devices.
Understanding IoT:
The seminar kicked off with an overview of IoT. As described by the presenter, IoT is a system of interrelated computing devices, mechanical and digital machines, objects, people or animals that are provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction. This interconnectedness allows for increased efficiency, accuracy, and economic benefit.
The Role of Arduino in IoT:
Transitioning seamlessly from the basic concepts of IoT, the presenter moved onto the key subject of the seminar: Arduino programming. Arduino, as I learned, is an open-source electronics platform based on easy-to-use hardware and software. It's designed around user-friendly hardware and software, making it an excellent tool for creating interactive projects.
Programming IoT devices with Arduino IDE:
The presenter emphasized the importance of Arduino IDE for programming IoT devices. The Arduino IDE, as elaborated in the seminar, is a cross-platform application that is written in the Java programming language. It is used for writing and uploading programs to Arduino compatible boards.
The presenter offered an engaging live demo that showcased programming an IoT device using the Arduino IDE. This part of the seminar was particularly illuminating as it provided a hands-on perspective of the programming process. The codes were well explained, and the presenter answered queries with a clarity that helped me understand the intricate connection between IoT and Arduino programming.
Concluding Remarks:
The seminar was an enriching experience that provided me with a greater understanding of the relationship between IoT and Arduino programming. It allowed me to gain an intimate knowledge of the practical aspects of IoT programming with Arduino IDE, and it was an invaluable opportunity to learn from an experienced professional in the field.
Photographic Journey:
Following are a series of photographs captured during the seminar, providing a visual journey through this insightful learning experience. These images serve as a testament to the depth and breadth of knowledge shared during the seminar, and the engaged, interactive nature of the presenter and audience.
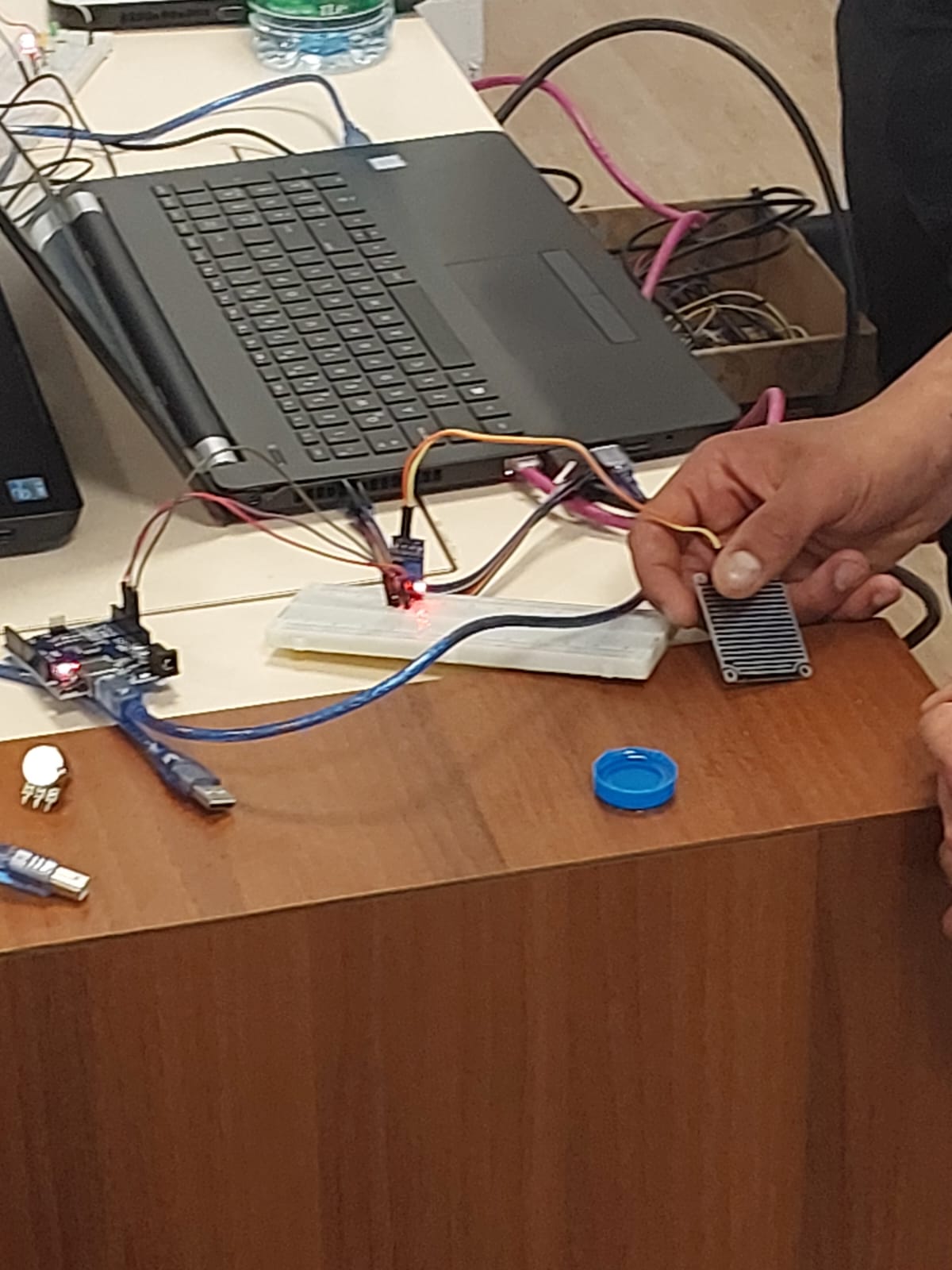

This enriching seminar has not only added value to my e-portfolio but has also broadened my horizon in the fascinating world of IoT and Arduino programming. I look forward to further exploration in this compelling field.